Mac Os Microsoft Au Daemon
In multitasking computer operating systems, a daemon (/ˈdiːmən/ or /ˈdeɪmən/)[1] is a computer program that runs as a background process, rather than being under the direct control of an interactive user. Traditionally, the process names of a daemon end with the letter d, for clarification that the process is in fact a daemon, and for differentiation between a daemon and a normal computer program. For example, syslogd is a daemon that implements system logging facility, and sshd is a daemon that serves incoming SSH connections.
In a Unix environment, the parent process of a daemon is often, but not always, the init process. A daemon is usually either created by a process forking a child process and then immediately exiting, thus causing init to adopt the child process, or by the init process directly launching the daemon. In addition, a daemon launched by forking and exiting typically must perform other operations, such as dissociating the process from any controlling terminal (tty). Such procedures are often implemented in various convenience routines such as daemon(3) in Unix.
Systems often start daemons at boot time which will respond to network requests, hardware activity, or other programs by performing some task. Daemons such as cron may also perform defined tasks at scheduled times.
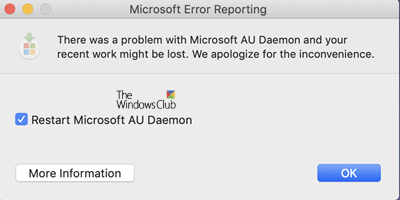
From my Ipad. I disregarded it, and waited it to go away until exiting Word.
Terminology[edit]
The term was coined by the programmers at MIT's Project MAC. They took the name from Maxwell's demon, an imaginary being from a thought experiment that constantly works in the background, sorting molecules.[2]Unix systems inherited this terminology. Maxwell's demon is consistent with Greek mythology's interpretation of a daemon as a supernatural being working in the background, with no particular bias towards good or evil. However, BSD and some of its derivatives have adopted a Christian demon as their mascot rather than a Greek daemon.[citation needed]
The word daemon is an alternative spelling of demon,[3] and is pronounced /ˈdiːmən/DEE-mən. In the context of computer software, the original pronunciation /ˈdiːmən/ has drifted to /ˈdeɪmən/DAY-mən for some speakers.[1]
Alternate terms for daemon are service (used in Windows, from Windows NT onwards — and later also in Linux), started task (IBM z/OS),[4] and ghost job (XDS UTS).
After the term was adopted for computer use, it was rationalized as a 'backronym' for Disk And Execution MONitor.[5]
Daemons which connect to a computer network are examples of network services.
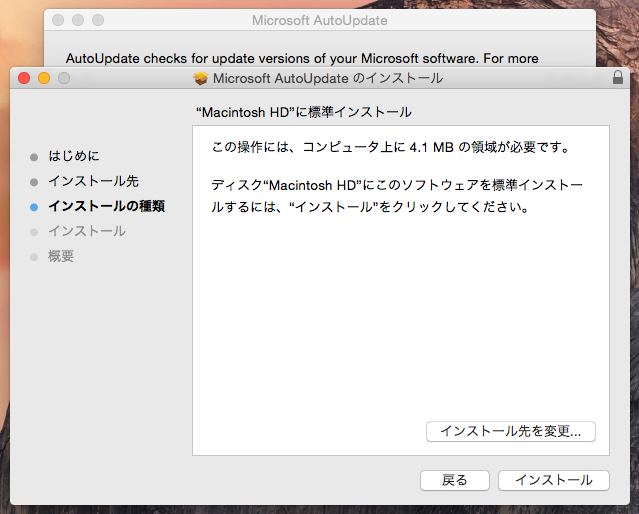
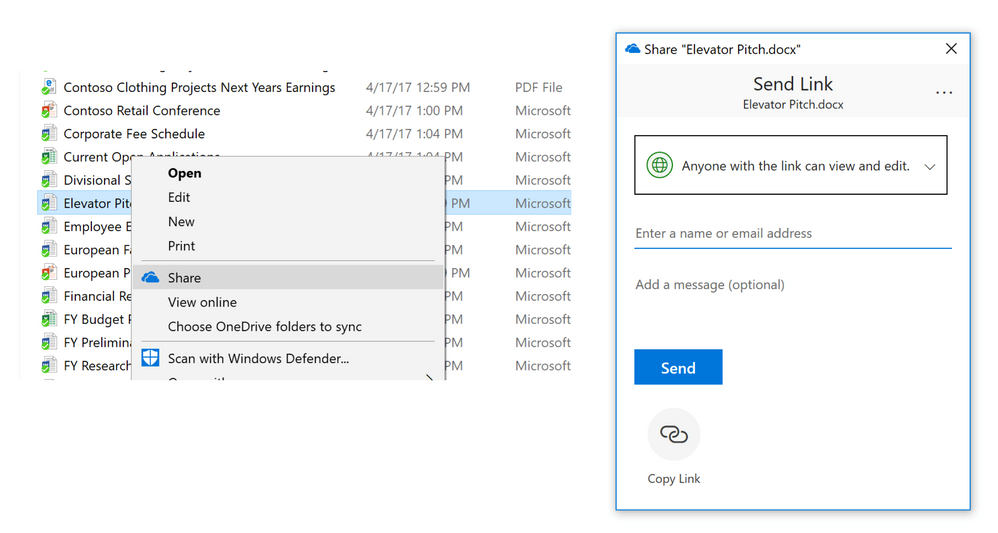
Microsoft AutoUpdate makes sure your copy of Office will always be up-to-date with the latest security fixes and improvements. If you are an Office 365 subscriber, you'll also receive the newest features and tools. If you downloaded Office from the Mac App Store, and have automatic updates turned on, your apps will update automatically. Office for Mac. Microsoft au daemon是干什么用的? 使用Macbook,发现进程里常有个叫Microsoft AU Daemon,却不知干什么用的。.
Implementations[edit]
Unix-like systems[edit]
In a strictly technical sense, a Unix-like system process is a daemon when its parent process terminates and the daemon is assigned the init process (process number 1) as its parent process and has no controlling terminal. However, more generally, a daemon may be any background process, whether a child of the init process or not.
On a Unix-like system, the common method for a process to become a daemon, when the process is started from the command line or from a startup script such as an init script or a SystemStarter script, involves:
- Optionally removing unnecessary variables from environment.
- Executing as a background task by forking and exiting (in the parent 'half' of the fork). This allows daemon's parent (shell or startup process) to receive exit notification and continue its normal execution.
- Detaching from the invoking session, usually accomplished by a single operation,
setsid():- Dissociating from the controlling tty.
- Creating a new session and becoming the session leader of that session.
- Becoming a process group leader.
- If the daemon wants to ensure that it won't acquire a new controlling tty even by accident (which happens when a session leader without a controlling tty opens a free tty), it may fork and exit again. This means that it is no longer a session leader in the new session, and can't acquire a controlling tty.
- Setting the root directory (/) as the current working directory so that the process does not keep any directory in use that may be on a mounted file system (allowing it to be unmounted).
- Changing the umask to 0 to allow
open(),creat(), and other operating system calls to provide their own permission masks and not to depend on the umask of the caller. - Closing all inherited files at the time of execution that are left open by the parent process, including file descriptors 0, 1 and 2 for the standard streams (stdin, stdout and stderr). Required files will be opened later.
- Using a logfile, the console, or /dev/null as stdin, stdout, and stderr.
If the process is started by a super-server daemon, such as inetd, launchd, or systemd, the super-server daemon will perform those functions for the process,[6][7][8] except for old-style daemons not converted to run under systemd and specified as Type=forking[8] and 'multi-threaded' datagram servers under inetd.[6]
MS-DOS[edit]
In the Microsoft DOS environment, daemon-like programs were implemented as terminate and stay resident (TSR) software.
Windows NT[edit]
On Microsoft Windows NT systems, programs called Windows services perform the functions of daemons. They run as processes, usually do not interact with the monitor, keyboard, and mouse, and may be launched by the operating system at boot time. In Windows 2000 and later versions, Windows services are configured and manually started and stopped using the Control Panel, a dedicated control/configuration program, the Service Controller component of the Service Control Manager (sc command), the net start and net stop commands or the PowerShell scripting system.
However, any Windows application can perform the role of a daemon, not just a service, and some Windows daemons have the option of running as a normal process.
Classic Mac OS and macOS[edit]
On the classic Mac OS, optional features and services were provided by files loaded at startup time that patched the operating system; these were known as system extensions and control panels. Later versions of classic Mac OS augmented these with fully fledged faceless background applications: regular applications that ran in the background. To the user, these were still described as regular system extensions.
What Is Microsoft Au Daemon For Mac
macOS, which is a Unix system, uses daemons. Note that macOS uses the term 'services' to designate software that performs functions selected from the Services menu, rather than using that term for daemons as Windows does.
Etymology[edit]
According to Fernando J. Corbató, who worked on Project MAC in 1963, his team was the first to use the term daemon, inspired by Maxwell's demon, an imaginary agent in physics and thermodynamics that helped to sort molecules, stating, 'We fancifully began to use the word daemon to describe background processes which worked tirelessly to perform system chores'.[9]
In the general sense, daemon is an older form of the word 'demon', from the Greek δαίμων. In the Unix System Administration HandbookEvi Nemeth states the following about daemons:[10]
Many people equate the word 'daemon' with the word 'demon', implying some kind of satanic connection between UNIX and the underworld. This is an egregious misunderstanding. 'Daemon' is actually a much older form of 'demon'; daemons have no particular bias towards good or evil, but rather serve to help define a person's character or personality. The ancient Greeks' concept of a 'personal daemon' was similar to the modern concept of a 'guardian angel'—eudaemonia is the state of being helped or protected by a kindly spirit. As a rule, UNIX systems seem to be infested with both daemons and demons.
A further characterization of the mythological symbolism is that a daemon is something which is not visible yet is always present and working its will. In the Theages, attributed to Plato, Socrates describes his own personal daemon to be something like the modern concept of a moral conscience: 'The favour of the gods has given me a marvelous gift, which has never left me since my childhood. It is a voice which, when it makes itself heard, deters me from what I am about to do and never urges me on'.[citation needed]
See also[edit]
- Bounce message (also known as mailer daemon)
References[edit]
- ^ abEric S. Raymond. 'daemon'. The Jargon File. Retrieved 2008-10-22.
- ^Fernando J. Corbató (2002-01-23). 'Take Our Word for It'. Retrieved 2006-08-20.
- ^'Merriam-Webster definition of daemon'. Merriam-Webster Online. Retrieved 2009-08-05.
- ^'IBM Knowledge Center - Glossary of z/OS terms and abbreviations'. IBM.
- ^'Daemon Definition'. www.linfo.org.
- ^ ab
inetd(8)– FreeBSD System Manager's Manual - ^
launchd.plist(5)– Darwin and macOS File Formats Manual - ^ ab'systemd.service'. freedesktop.org. Retrieved August 25, 2012.
- ^'The Origin of the word Daemon'.
- ^'The BSD Daemon'. Freebsd.org. Retrieved 2008-11-15.
External links[edit]
Applies to:
Collecting diagnostic information
If you can reproduce a problem, please increase the logging level, run the system for some time, and restore the logging level to the default.
Increase logging level:
Reproduce the problem Microsoft edge macos.
Run
sudo mdatp --diagnostic --createto backup Microsoft Defender ATP's logs. The files will be stored inside of a .zip archive. This command will also print out the file path to the backup after the operation succeeds.Restore logging level:
Logging installation issues
If an error occurs during installation, the installer will only report a general failure.
The detailed log will be saved to /Library/Logs/Microsoft/mdatp/install.log. If you experience issues during installation, send us this file so we can help diagnose the cause.
Uninstalling
There are several ways to uninstall Microsoft Defender ATP for Mac. Please note that while centrally managed uninstall is available on JAMF, it is not yet available for Microsoft Intune.
Interactive uninstallation
- Open Finder > Applications. Right click on Microsoft Defender ATP > Move to Trash.
From the command line
sudo rm -rf '/Applications/Microsoft Defender ATP.app'sudo rm -rf '/Library/Application Support/Microsoft/Defender/'
Configuring from the command line
Important tasks, such as controlling product settings and triggering on-demand scans, can be done from the command line:
| Group | Scenario | Command |
|---|---|---|
| Configuration | Turn on/off real-time protection | mdatp --config realTimeProtectionEnabled [true/false] |
| Configuration | Turn on/off cloud protection | mdatp --config cloudEnabled [true/false] |
| Configuration | Turn on/off product diagnostics | mdatp --config cloudDiagnosticEnabled [true/false] |
| Configuration | Turn on/off automatic sample submission | mdatp --config cloudAutomaticSampleSubmission [true/false] |
| Configuration | Turn on PUA protection | mdatp --threat --type-handling potentially_unwanted_application block |
| Configuration | Turn off PUA protection | mdatp --threat --type-handling potentially_unwanted_application off |
| Configuration | Turn on audit mode for PUA protection | mdatp --threat --type-handling potentially_unwanted_application audit |
| Diagnostics | Change the log level | mdatp --log-level [error/warning/info/verbose] |
| Diagnostics | Generate diagnostic logs | mdatp --diagnostic --create |
| Health | Check the product's health | mdatp --health |
| Protection | Scan a path | mdatp --scan --path [path] |
| Protection | Do a quick scan | mdatp --scan --quick |
| Protection | Do a full scan | mdatp --scan --full |
| Protection | Cancel an ongoing on-demand scan | mdatp --scan --cancel |
| Protection | Request a security intelligence update | mdatp --definition-update |
| EDR | Turn on/off EDR preview for Mac | mdatp --edr --early-preview [true/false] OR mdatp --edr --earlyPreview [true/false] for versions earlier than 100.78.0 |
| EDR | Add group tag to machine. EDR tags are used for managing machine groups. For more information, please visit https://docs.microsoft.com/windows/security/threat-protection/microsoft-defender-atp/machine-groups | mdatp --edr --set-tag GROUP [name] |
| EDR | Remove group tag from machine | mdatp --edr --remove-tag [name] |
Client Microsoft Defender ATP quarantine directory
/Library/Application Support/Microsoft/Defender/quarantine/ contains the files quarantined by mdatp. The files are named after the threat trackingId. The current trackingIds is shown with mdatp --threat --list --pretty.
Microsoft Defender ATP portal information
Microsoft Daemon For Mac
This blog provides detailed guidance on what to expect in Microsoft Defender ATP Security Center.